Blog
Cybersecurity solutions to prevent and protect against computer attacks
Cybersecurity solutions to prevent and protect against computer attacks
Faced with the complexity and proliferation of cyber-attacks in recent years, it is essential to protect your information system by putting in place appropriate resources.
Prevention rules and raising awareness of good security practices remain the number one barrier to blocking a potential computer attack :
- Remain vigilant when receiving emails,
- Protect access with two-factor authentication,
- Use complex passwords,
- Always keep your operating system up to date.
The introduction of new cybersecurity solutions provides new ways of protecting against potential cyber-attacks.
Professional antivirus solutions :
The first of these is the use of professional anti-virus solutions, which use a regularly updated virus database to protect your computers from potential attacks.
Depending on the version and your applications, these solutions can protect systems right up to the Microsoft 365 suite, using advanced defence tools such as :
- Setting up a Sandbox to receive attachments from the publisher upstream so that they can be checked.
- Identifying Ransomware, email identity theft, phishing and advanced targeted attacks.

Firewalls :
The second method is to install firewalls, which are tools for monitoring and filtering data flows passing over the network or coming from external sources. These are particularly useful with the widespread use of teleworking in recent years: employees connecting from outside to the company’s internal network are connected securely by having their data flows encrypted via the firewall.
Endpoint Detection and Response (EDR) :
In response to the growing complexity of computer attacks, new tools have been developed for endpoints: Endpoint Detection and Response (EDR). These intelligent systems use behavioural analysis of the computer workstation to detect and analyse suspicious activity (in a more advanced way than conventional anti-virus software) and inform the teams responsible for IT security, so they can take rapid decisions to stop a potential attack.

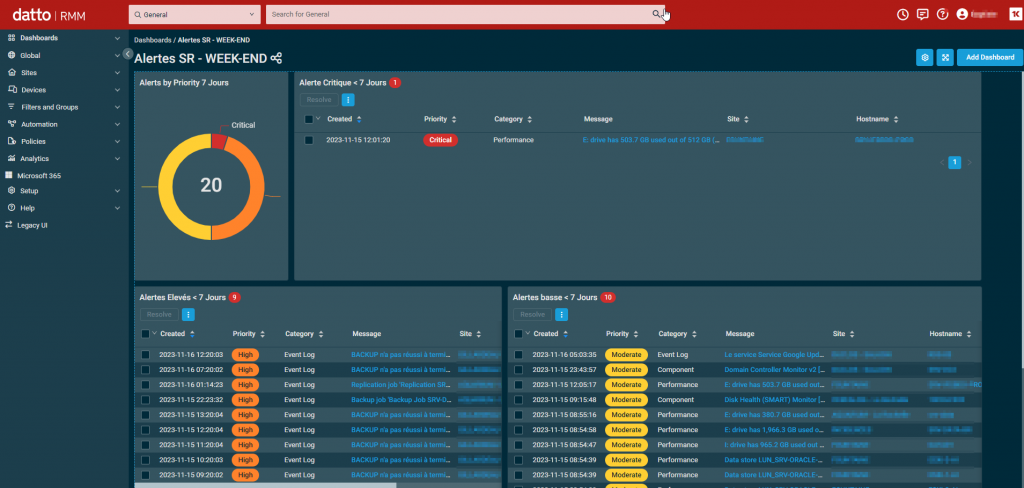
RMM (Remote Monitoring and Management) software :
The adoption by the company’s IT department of “RMM” type software (short for Remote Monitoring and Management) also makes it possible to participate in the general security of the information system.
These tools enable the integrity of the systems connected to them to be monitored remotely.
They can also be used to automate certain processes, such as deploying certain software remotely, connecting to remote machines for troubleshooting, running scripts for deployment, but above all, they can be used to check that patches and security updates from different products (Microsoft, Adobe, etc.) are being applied correctly.
Thanks to a centralised console, this tool provides accurate reporting on the health of the IT estate on a single screen.

Do you have any questions about one of these solutions?
